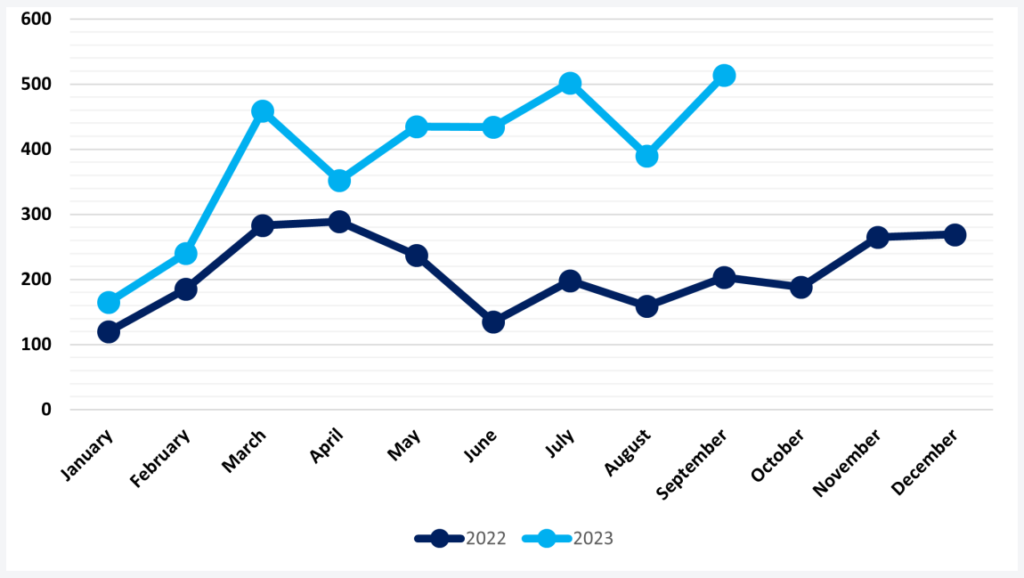
Ransomware incidents reached an unprecedented peak in September, following a relatively quieter period in August, which still exceeded the usual standards for the summer months.
As per data from NCC Group, there were a total of 514 ransomware attacks launched in September. This figure surpasses the level of activity seen in March 2023, which recorded 459 attacks, with a significant focus on data theft attacks by the Clop group.
Notably, Clop exhibited minimal activity in September, potentially indicating that this sophisticated ransomware gang is gearing up for a significant upcoming attack.
However, the record number of attacks in September was primarily attributed to other threat groups, with LockBit 3.0 leading with 79 attacks, followed by LostTrust with 53 attacks, and BlackCat with 47 attacks.
Emerging Players in the Field
Recently formed threat actor LostTrust ranked as the second most active group, responsible for 53 (10%) of all attacks, with another new group – RansomedVC – in fourth place with 44 (9%) attacks.
LostTrust is believed to have formed in March this year, with activity now coming to light in September. The group has adopted similar methods of double extortion used widely by more established threats.
Well-established threat actors remained active in September, with Lockbit retaining its August top spot. With new threat actors emerging and following the decrease of its activity in August, Cl0p was only responsible for three ransomware attacks in September, according to NCC Group’s data.
Ransomware in Western Regions
Consistent with patterns from previous months, North America sustained its position as the primary target for ransomware attacks, with 258 incidents occurring in September. Europe held its status as the second most targeted region, experiencing 155 attacks, followed by Asia in third place with 47 attacks.
Nevertheless, September witnessed a 3% rise in attacks targeting North America and a 2% increase in Europe, while the number of attacks in Asia decreased by 6% compared to August.
These statistics suggest an escalating interest from threat actors in directing their efforts toward Western regions.
In terms of targeted regions, North America took the lion’s share with 50%, Europe followed with 30%, and Asia was third with 9%.
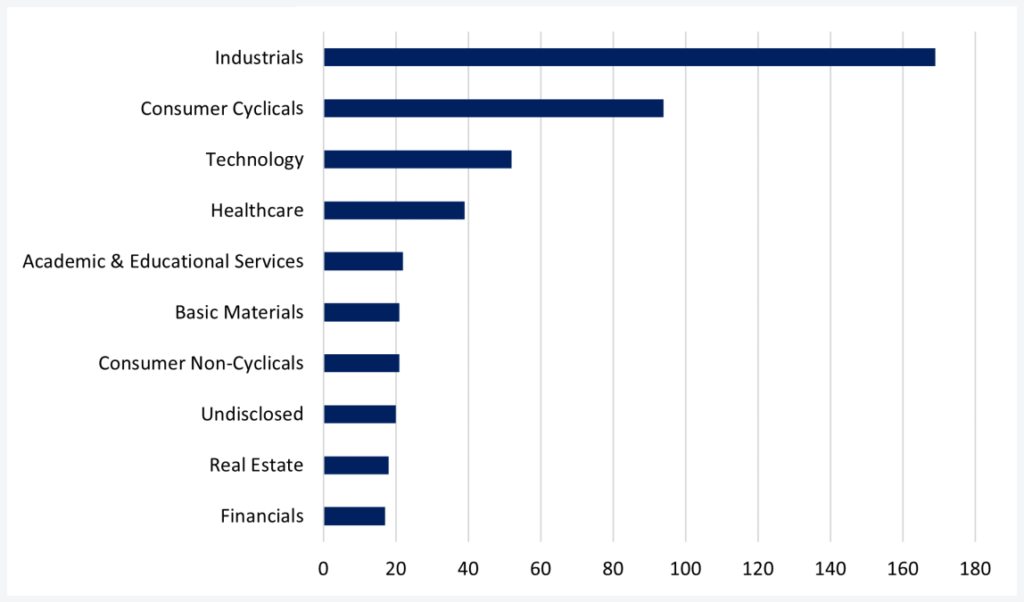
The most targeted sectors were ‘industrials’ (construction, engineering, commercial services) with 169 attacks, ‘consumer cyclicals’ (retail, media, hotels) with 94, technology (software and IT services, networking, telecommunications) with 52, and healthcare with 38.
Heightened Activity in Targeting Healthcare
In September, the Industrials sector maintained the highest incidence of attacks at 40% (19 attacks), followed by Consumer Cyclicals at 21% (10 attacks), and Healthcare at 15% (7 attacks).
The persistent focus on Industrials comes as no surprise, as the theft of Personally Identifiable Information (PII) and Intellectual Property (IP) remains enticing for threat actors.
The Healthcare sector witnessed a substantial surge in ransomware attacks, recording a total of 18 attacks, representing an 86% increase compared to the previous month, August. However, this upswing aligns with trends observed in earlier months this year, indicating that the dip in August was an anomaly within the broader pattern.
Healthcare remains an appealing target for threat actors, particularly due to the significant financial impact that a ransomware attack on pharmaceutical companies can potentially inflict.
2023 on an Unprecedented Course
The NCC’s report emphasizes that between January 2023 and September 2023, approximately 3,500 attacks were documented, and it is now highly likely that the final count will approach 4,000 by year-end.
An earlier report from Chainalysis in the same year anticipated that 2023 would establish records in ransomware payments based on their projected data.
Despite ongoing law enforcement endeavors to address this issue, which has grown more sophisticated, ransomware endures as a constantly evolving menace that inundates organizations with continually refined means of initial access and progressively concealed techniques and payloads.
Sources :